Litecoin Reorg Undoes Attack as Earlier Patch Timeline Raises Questions
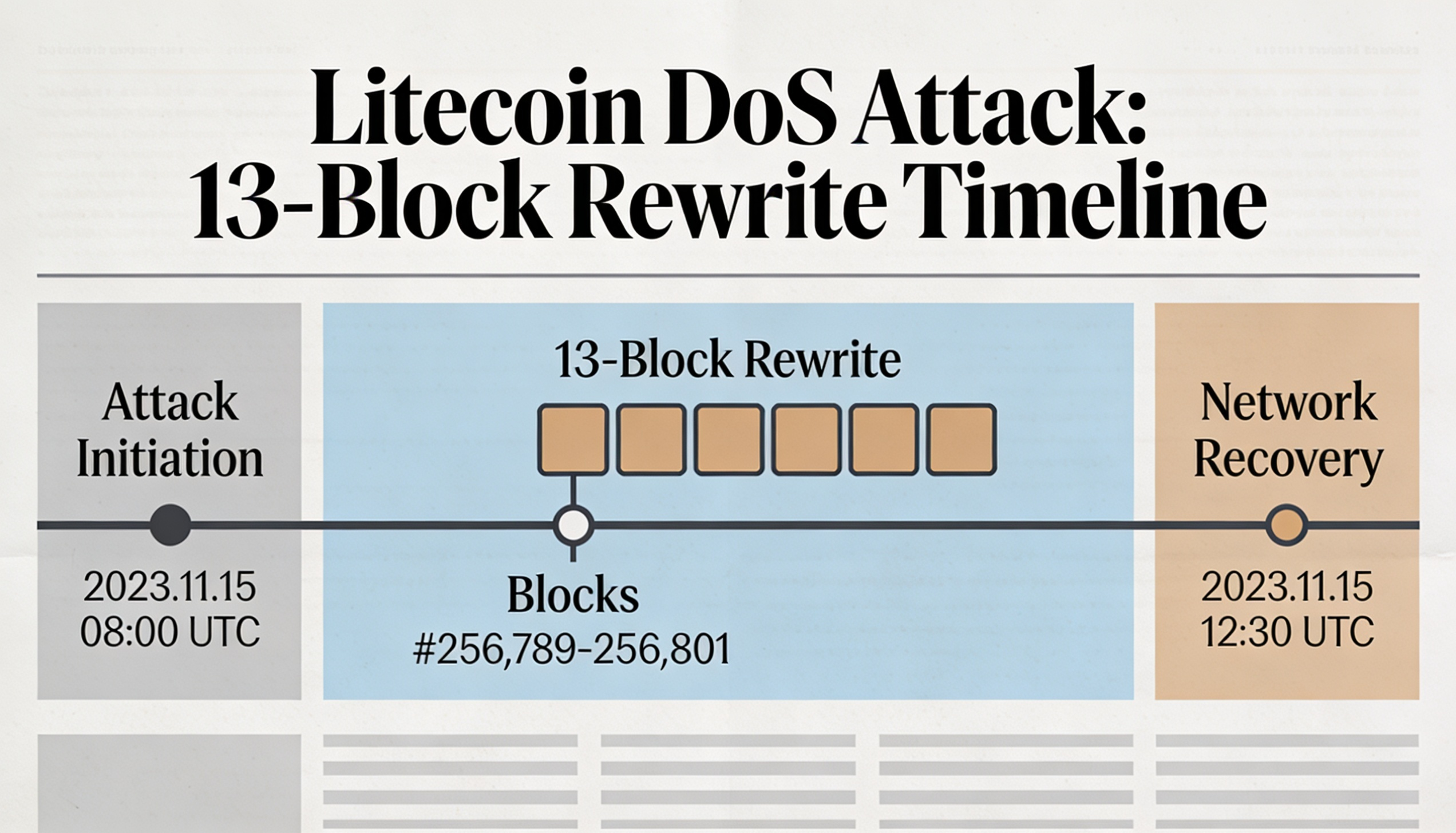
Litecoin rolled back 13 blocks late Friday into Saturday, wiping out about 30 minutes of transactions after a vulnerability in its Mimblewimble Extension Block (MWEB) feature was exploited.
The flaw allowed invalid MWEB transactions to pass through nodes running outdated software, enabling a denial-of-service (DoS) attack that affected major mining pools. The network ultimately resolved the issue by reverting to the longest valid chain.
The Litecoin Foundation described the incident as a zero-day and said Sunday that the network had been fully patched and was operating normally.
However, a review of the litecoin-project’s public GitHub commits suggests the core vulnerability had been identified and fixed weeks before the attack. Security researcher “bbsz” of SEAL911 highlighted that the consensus flaw enabling invalid MWEB peg-outs was patched between March 19 and March 26.
A separate DoS-related issue was addressed on April 25, with both fixes later bundled into release 0.21.5.4 — after the attack was already in progress.
The timeline indicates that while the vulnerability had been resolved at the code level, the fix had not been broadly rolled out across the network, leaving some participants exposed.
The episode highlights a key challenge for decentralized systems: even when critical bugs are fixed, delayed adoption can allow exploits to slip through.